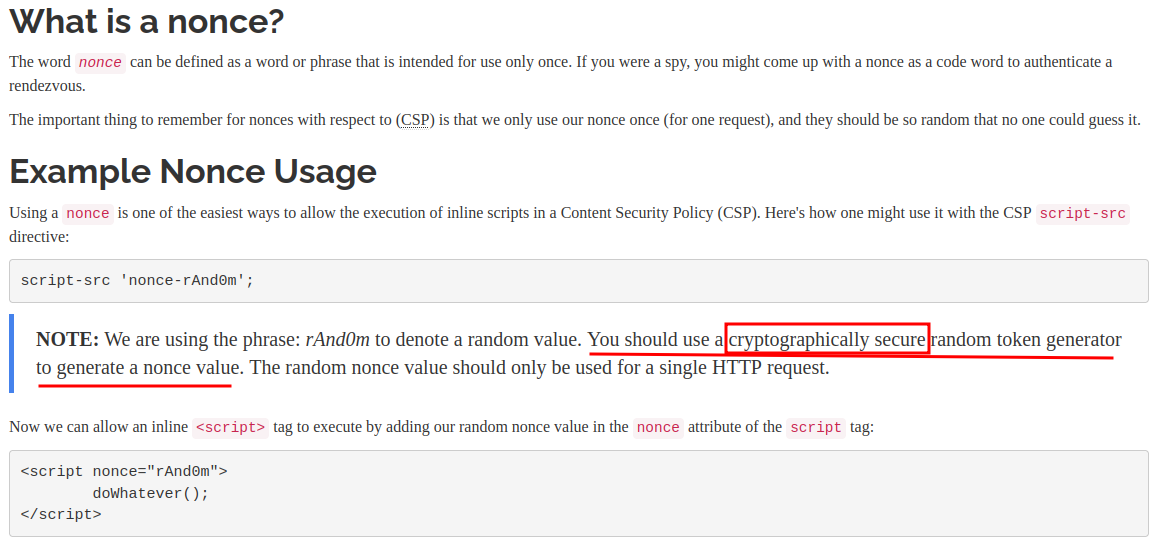
⚖ The 'nonce-value' allows any host-sources for external scripts and allows inline scripts without 'unsafe-inline' in the script-src, 'nonce-value' is case-sensitive
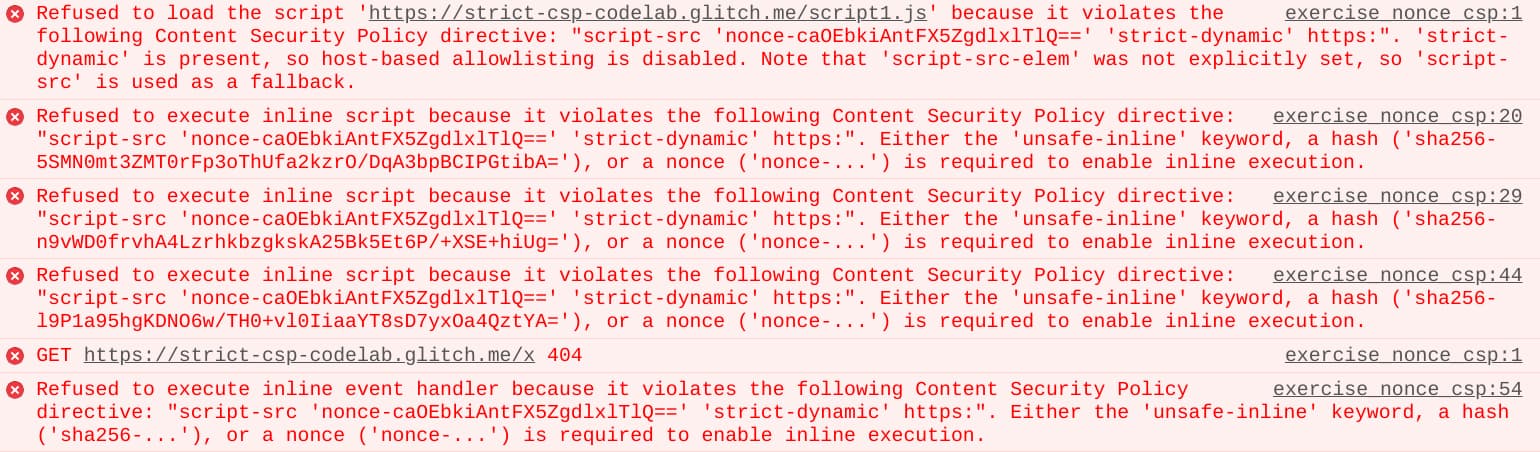
Mitigate cross-site scripting (XSS) with a strict Content Security Policy ( CSP) | Articles | web.dev

⚖ CSP: the 'nonce-value' allows external stylesheets from any sources and allows inline styles without 'unsafe-inline' in the style-src, but does not allow @import; 'nonce-value' is case-sensitive

⚖ The 'nonce-value' allows any host-sources for external scripts and allows inline scripts without 'unsafe-inline' in the script-src, 'nonce-value' is case-sensitive
GitHub - MarcelloTheArcane/netlify-plugin-csp-generator: Generate CSP headers from inline script hashes

Parse Dashboard 5.0.0 / Insecure ContentSecurityPolicy (CSP) - Parse Dashboard - Parse Community Forum
GitHub - moveyourdigital/cloudflare-worker-csp-nonce: A Cloudflare worker to generate and inject Content Security Policy nonces in returned HTML pages.
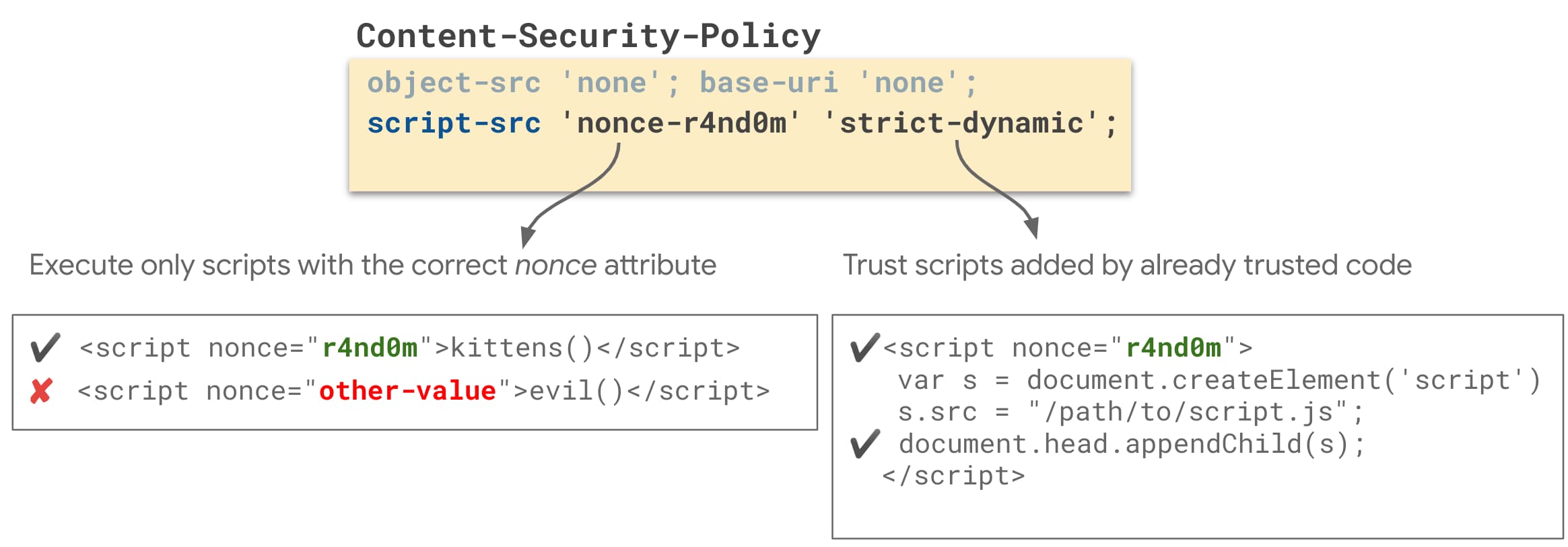
Mitigate cross-site scripting (XSS) with a strict Content Security Policy ( CSP) | Articles | web.dev

⚖ Content Security Policy: both 'nonce-value' and 'hash-value' in the style-src directive, which one is higher priority

⚖ The 'nonce-value' allows any host-sources for external scripts and allows inline scripts without 'unsafe-inline' in the script-src, 'nonce-value' is case-sensitive

Mitigate cross-site scripting (XSS) with a strict Content Security Policy ( CSP) | Articles | web.dev